Fraud Management & Cybercrime,
Social Engineering
Chinese-Speaking Operators Have Positioned Lucid as a Key Player in Phishing Campaigns
Recent analyses from security experts indicate an imminent spike in text message phishing, commonly referred to as smishing, driven by a phishing-as-a-service (PhaaS) platform known as Lucid. This system is reportedly operated by Chinese-speaking threat entities and is believed to be facilitating extensive campaigns across 88 countries.
Lucid stands out for its ability to spread malicious links through platforms such as Apple iMessage and Rich Communication Services on Android. What sets it apart is an integrated credit card generator, which aids cybercriminals in the validation of stolen payment information, enhancing its efficacy in fraudulent activities.
This platform has rapidly evolved into a primary source of phishing campaigns targeting users in regions including Europe, the United Kingdom, and the United States. Initially localized, Lucid’s influence has expanded significantly, with researchers at threat intelligence firm Catalyst projecting a notable increase in its impact by early 2025.
Operated on a subscription basis, Lucid allows cybercriminals to deploy automated and customizable phishing attacks. This operation offers sophisticated anti-detection tactics, such as IP blocking and user-agent filtering, which serve to extend the operational life of phishing websites.
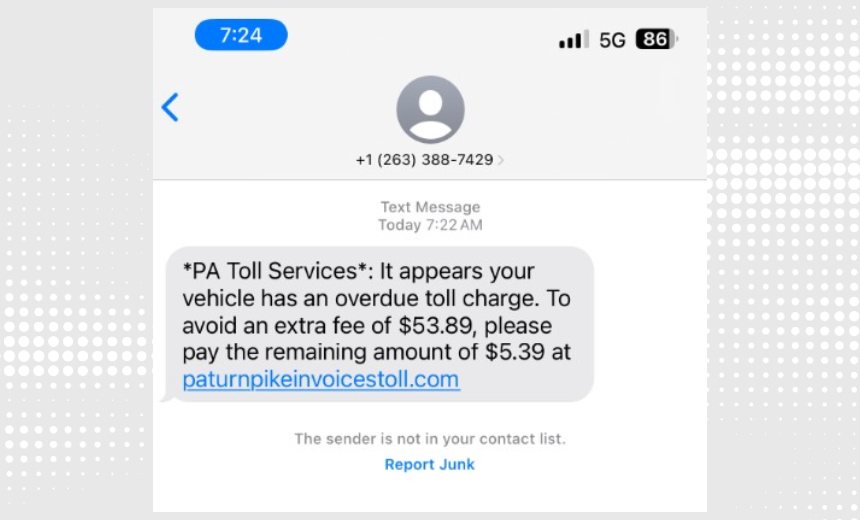
The group behind Lucid, often referred to as “Black Technology” or “XinXin,” has been actively involved in cybercrime since 2023, predominantly focusing on the theft of credit card data and personally identifiable information via deceptive texts purportedly from legitimate avenues, such as postal and courier services, as well as government agencies. Reports have suggested a surge in smishing incidents in the U.S., with scams falsely claiming to originate from road toll collection services. The FBI issued a warning regarding this fraudulent scheme in 2024, and further alerts have followed from federal and state authorities, underscoring the pervasive nature of this threat.
Operational data from Catalyst indicates that campaigns utilizing Lucid exhibit an approximate success rate of 5%. The platform itself operates via internet channels rather than traditional telecom networks, which not only enhances message delivery rates but also allows attackers to circumvent telecom filtering measures. Lucid employs advanced obfuscation techniques, including time-sensitive URLs and device fingerprinting, to avoid detection by security analysts and automated threat intelligence systems.
Additionally, the phishing pages generated are tailored to the geographical location of victims, thereby mimicking local organizations to further increase credibility. The system also harnesses automated tools, enabling attackers to efficiently design and disseminate phishing campaigns with minimal effort and expertise required.
Lucid provides a comprehensive attack infrastructure, with threat actors sourcing phone numbers through data breaches, open-source intelligence, and underground markets. It competes with other PhaaS platforms, like Darcula and Lighthouse, positioning itself as a significant player in the cybercrime landscape.
The operators of Lucid actively promote their services on platforms such as Telegram, boasting capabilities to dispatch over 100,000 smishing messages daily. This hierarchical system allows for diverse roles within the operation, including administrators and guests, and licenses for access are sold on a weekly renewal basis, with automatic suspensions for non-renewal.
In examining the tactics likely employed by Lucid, the MITRE ATT&CK Matrix suggests initial access methods such as phishing, as well as persistence techniques, including credential dumping. As the threat landscape evolves, businesses are urged to remain vigilant, enhance their cybersecurity measures, and stay informed about the latest developments in these sophisticated threats.